What is two-factor authentication?
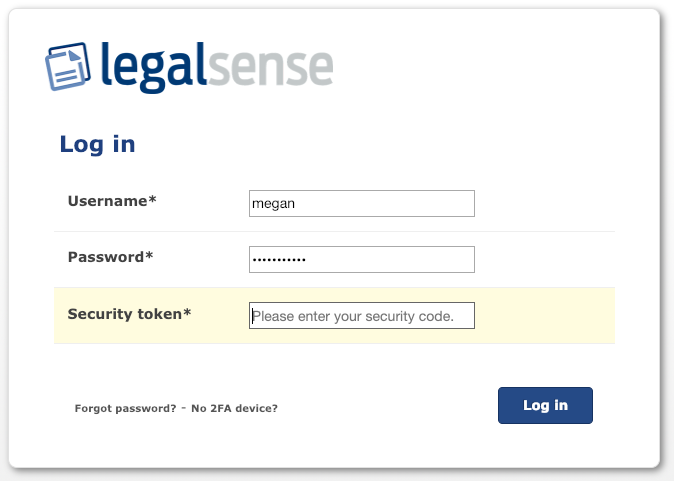
Two-factor authentication (herafter 2FA) is an authentication method where two factors must be present in order to access Legalsense. The first factor is - in Legalsense's case - entering a user name and password. The second factor is a code on a chosen device via, for example, the Google Authenticator or Microsoft authenticator app or a password manager such as 1Password. Only this combination gives access to Legalsense. Therefore, two components are required to gain access.
How to configure 2FA
As a user you can always configure the 2FA extra security step for your own account (unless this is enforced centrally by the office).
Adding a 2FA device on your own initiative
If 2FA is not mandatory within the office, you as a user can choose to use it. To set this up, go to your Account (top right next to your username):
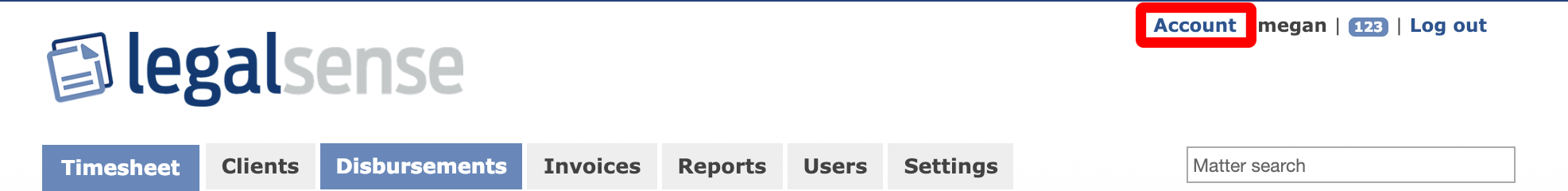
On the "My account" page, the second section is the 'Two factor authentication' part.
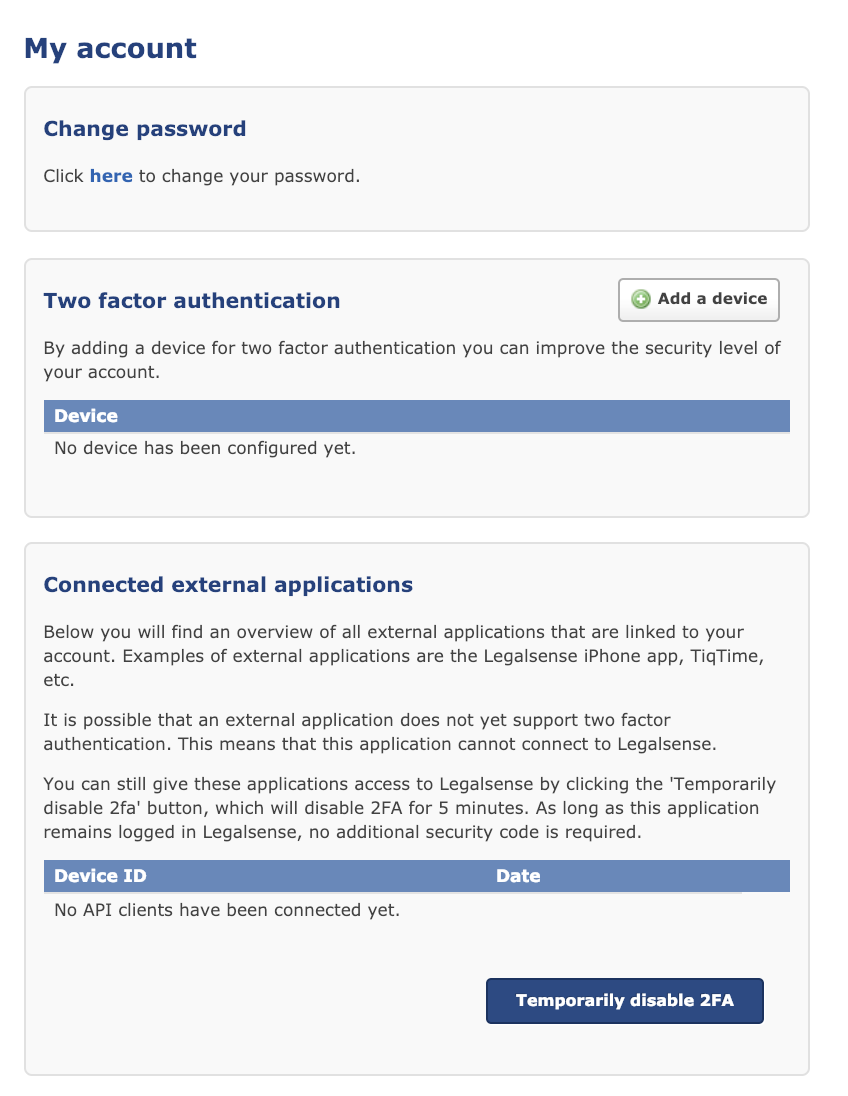
On this page you can add a 2FA device by clicking "Add a device":
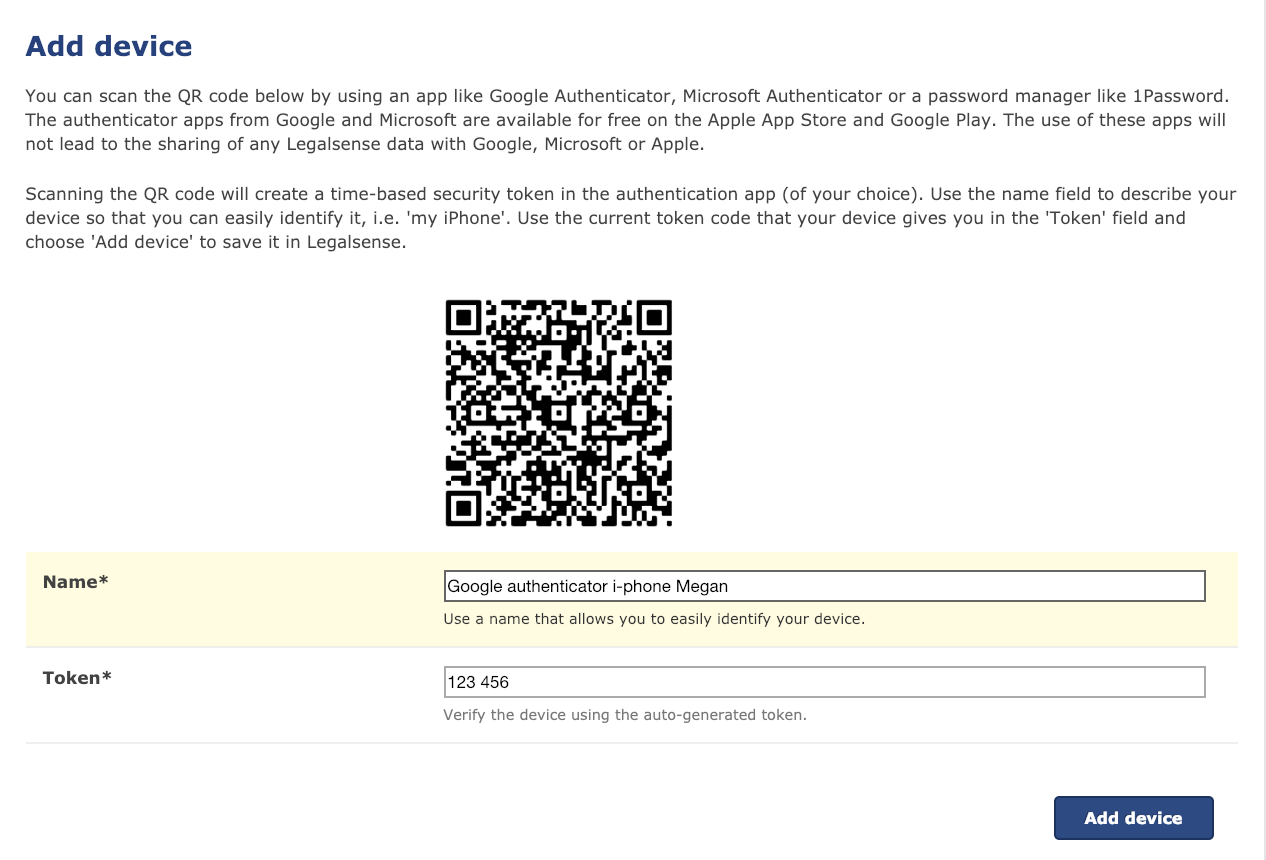
After you have entered the data and clicked on "Add Device", you can use the device to log in to Legalsense.
Removing a 2FA device on your own initiative
If you want to stop using 2FA (and it is not enforced centrally) you can do so on the 'My Account' page by deleting your devices. When you delete all devices, 2FA will be disabled automatically. You can then log in again with only username and password.
Sometimes your browser still incorrectly displays the third entry field with the security code after having removed all devices. If this is the case, you can remove the cache from your browser, after which you will be shown the standard login screen with two input fields again.
Operation of 2FA if the office has enforced this centrally.
If the office has set up 2FA centrally (see the article Two-factor authentication setup for administrators) you will, after logging on, be shown a screen where you can enter your e-mail address. This is where the instructions for creating a 2FA device will be sent to:
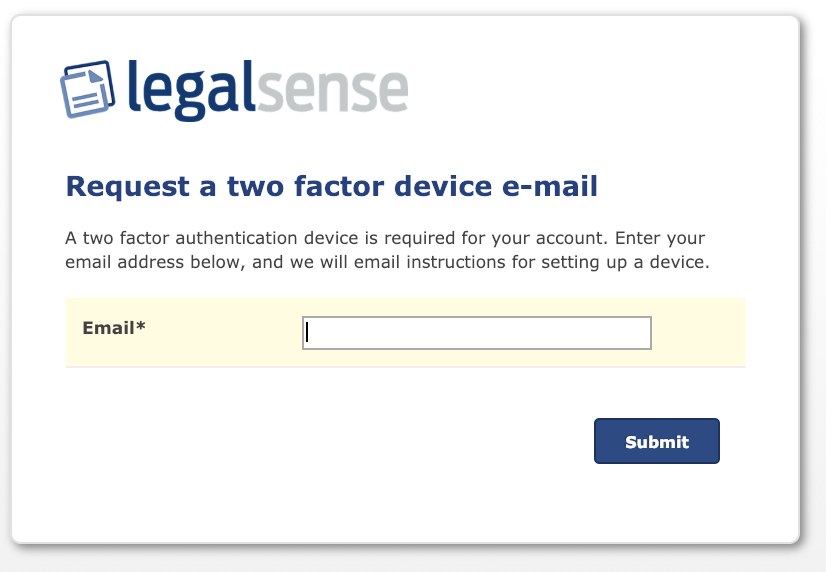
Please note that this email address must be equal to the email address of your Legalsense account.
After entering your e-mail address, you will receive an e-mail with instructions and a link to set up a 2FA device. If you click on the link in the email, you will see the following instruction:
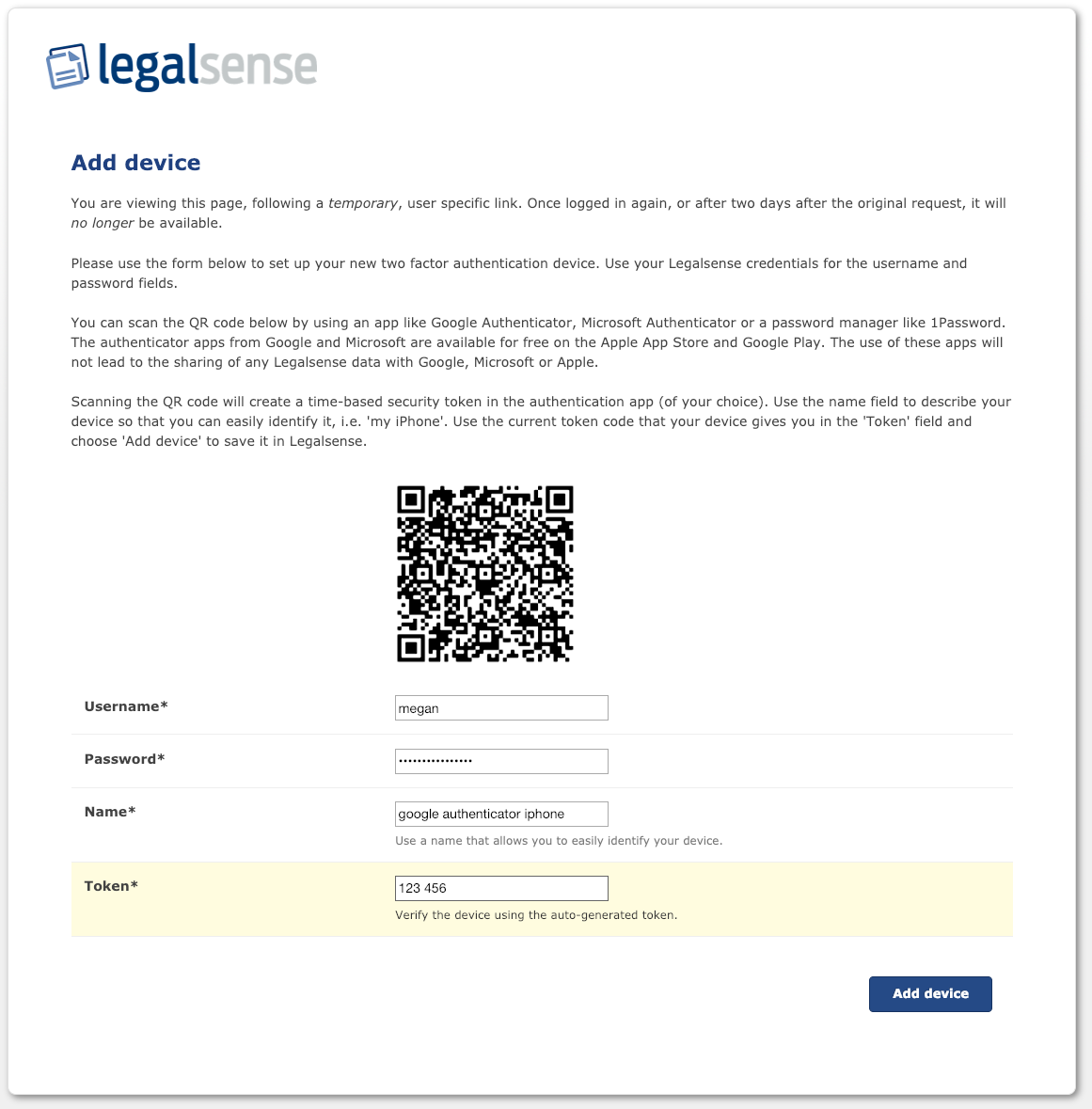
After filling in the required information successfully, you will see the following confirmation:
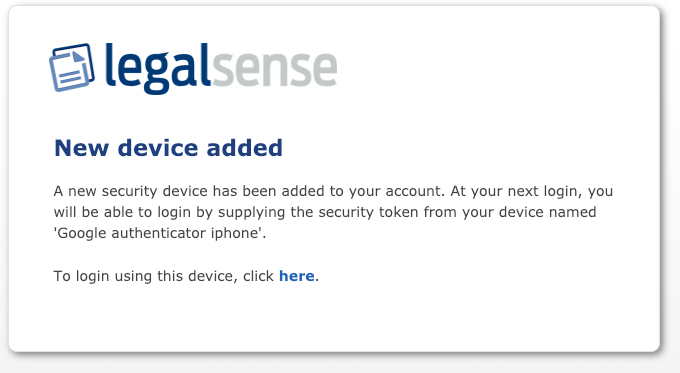
From now on you can log on only with the use of the added device.
Managing devices
You can manage your devices via the "My account" page:
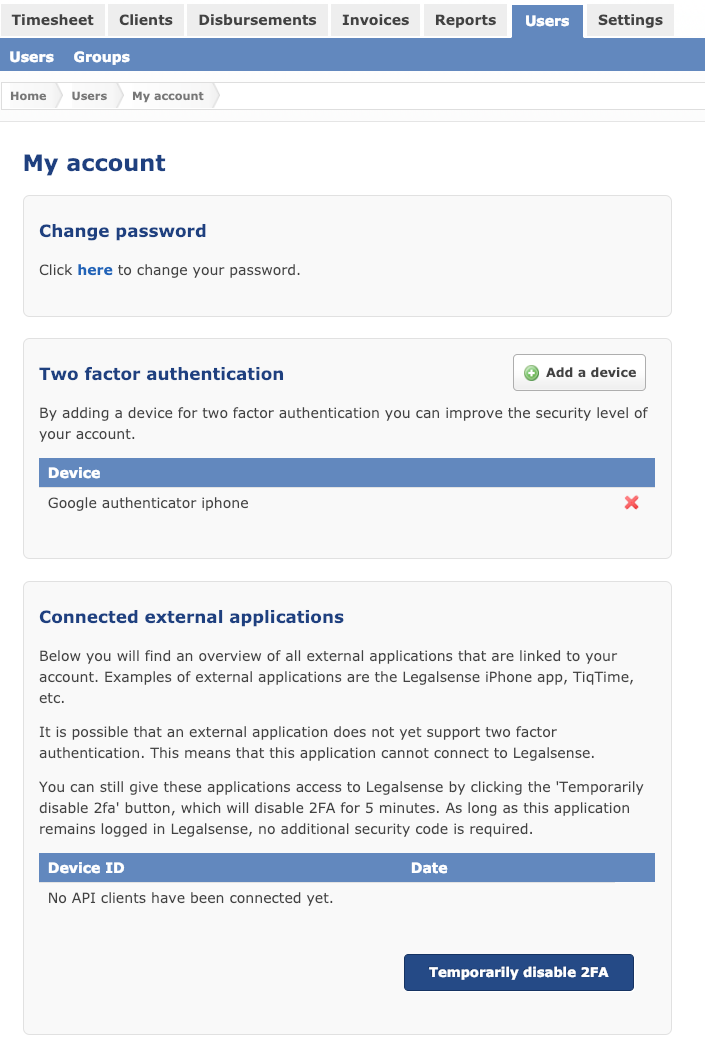
It is possible to connect multiple 2FA devices to your account. For example, you can connect an app on your smartphone user (e.g. Microsoft authenticator) and a password manager as 1Password. You can delete devices by clicking on the delete icon (red cross) behind the device.
2FA and the Legalsense iOS app or other external applications
If you are using the Legalsense iOS app or another external application (for example Tiq Time) you will see these applications on the "My Account" page under "Associated External Applications". If the external application does not yet have support to log in with 2FA (within Legalsense) there is an extra option available to temporarily disable 2FA (by pressing that button). For example, you can then log in to the Legalsense iPhone app and as long as you do not explicitly choose to log out, you will remain logged in.
Please note that an update of the Legalsense iOS (iPhone) app is ready that allows you to log in with a 2FA code. This update will soon be available in the App store. The temporary deactivation of 2FA for (one-time) login in the Legalsense app is then no longer necessary.

Comments
0 comments
Please sign in to leave a comment.